Cybersecurity is a serious threat to all organizations. Hackers can randomly attack any business as long as you have internet access. Once they are able to attack a business and find a vulnerability they can hold your data hostage, sell it on the black market or do whatever they want with it. No one wants to pay hackers to get their own data back but they realize if they can attack hundreds or thousands or companies they will get money (and not get caught). This is what makes them do what they do. Here is an article on October 26, 1018 from WBAL “Cyber Firm Claims To Have Hacked Into Democratic Fundraising Files In Maryland” regarding election data breaches. Advantage is here to help. Our security and vulnerability service will scan your network for security threats and vulnerabilities and also do a dark web search for any activity. Our tools detect open security vulnerabilities across your entire network, and it will also search all devices across your network for malware infections and threats.
With our vulnerability scan we will:

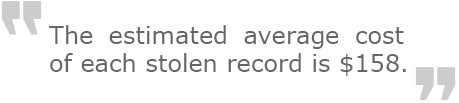
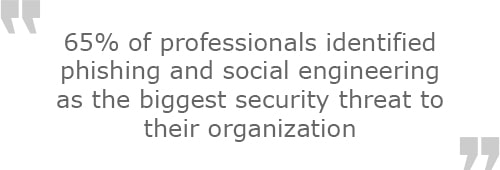
 Every company should take security seriously. Cybersecurity is a growing threat across the world and cyber criminals are looking to take advantage of anyone they can. Recent news headlines have shown data breaches targeting companies like Facebook, Under Armour, Panera, & Ticketfly. Attacks don’t just happen to large corporations, they happened to organizations of all sizes especially small businesses. 62% of all cybersecurity attacks are done to small and medium businesses. Why is that? Well if you think about large corporations they have more resources, available funds, and need to answer to more people so they do not have as many security breaches (although they get attacked constantly). When a small or medium business is attacked a majority of the time they do not even know they were attacked, have the resources to identify it, or have the staffing resources with the security skill-set. Your most important asset next to your employees is your data.
Every company should take security seriously. Cybersecurity is a growing threat across the world and cyber criminals are looking to take advantage of anyone they can. Recent news headlines have shown data breaches targeting companies like Facebook, Under Armour, Panera, & Ticketfly. Attacks don’t just happen to large corporations, they happened to organizations of all sizes especially small businesses. 62% of all cybersecurity attacks are done to small and medium businesses. Why is that? Well if you think about large corporations they have more resources, available funds, and need to answer to more people so they do not have as many security breaches (although they get attacked constantly). When a small or medium business is attacked a majority of the time they do not even know they were attacked, have the resources to identify it, or have the staffing resources with the security skill-set. Your most important asset next to your employees is your data. 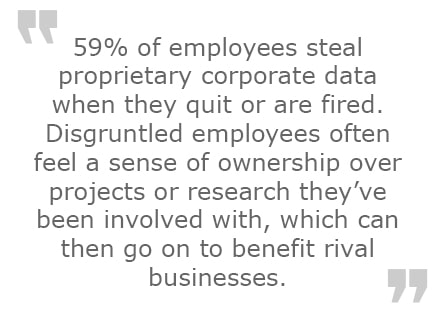
Doing a vulnerability scan is an effective way for Advantage to demonstrate the value we deliver to our clients without any risk to you. We feel that if you are satisfied with our services on identifying potential security problems, you will consider us to work with in the future. This is a lot more effective than having a heavy sales tactic or having something thrown in your face. At Advantage Industries, we are committed to providing each client with high-quality technology assistance and services that are just a phone call away.
Getting started is easy. Contact us today by calling us at 866-443-8238 or by filling out the form on the right side. From there we can schedule a time for a vulnerability scan. We will provide you with more information on how we perform the scan and ask for specific information including a list of email addresses/domains you would like us to test. After we do our scan, we will then prepare the results and go over the report with you, discuss our findings, show how to resolve the issues and answer any questions you may have.

Keith Heilveil

Sr. Director of Sales, PMP