What You Need To Know About Phishing
You’re reading this article, which means you may have been a victim of phishing recently. If so, don’t feel bad, you’re not alone: 65% of organizations in the US have been hit by phishing.
And even if you haven’t been hit, you’ve definitely been a target. There are simply too many phishing emails being sent every day for you to avoid it – back in April, Google blocked 240 million phishing emails related to COVID-19 in one week alone.
The bottom line is that you can’t ignore the threat of phishing, and by reading this blog, you’re not. And luckily for you, protecting against phishing doesn’t mean you have to understand how to install and configure a complex firewall, or shell out for a next-generation cybersecurity solution.
Protecting against phishing comes down to what you know…
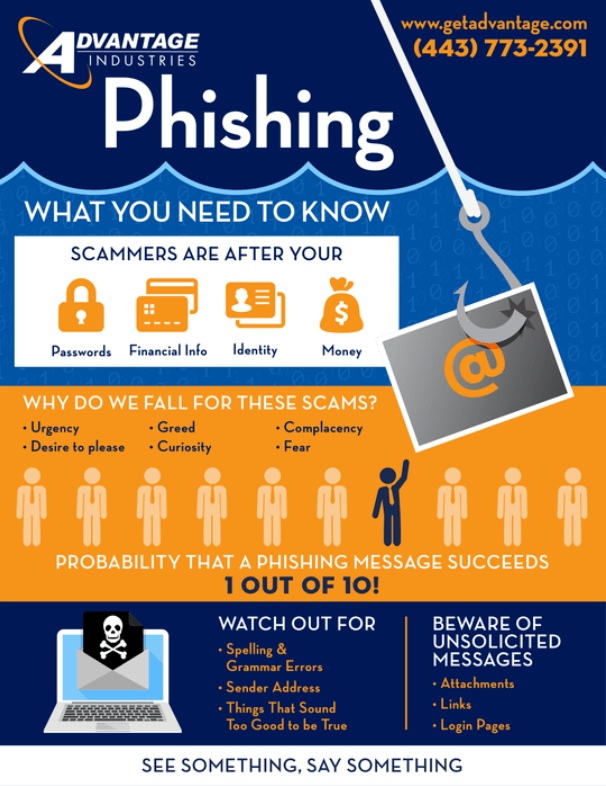
Click Here To Download This Infographic
How Does Phishing Work?
Phishing is a method in which cybercriminals send fraudulent emails that appear to be from reputable sources in order to steal one or both of the following assets:
- Information: Whether it’s your passwords, financial information, or private identification information, it all has value to cybercriminals.
- Money: Some phishing emails will trick you into executing a wire transfer, fulfilling a false invoice, or providing access to personal or company funds.
What Makes You An Easy Target For Phishing?
Phishing is a social engineering method, which means it takes advantage of people, not technology. Instead of finding a vulnerability in your firewall, phishing exploits an ignorant user.
Effective phishing scams take advantage of…
- Your Fear: If the subject line makes it sound like an emergency — “Your account has been suspended”, or “You’re being hacked” — that’s a red flag. It’s in the scammer’s interest to make you panic and move quickly, which might lead to you overlooking other indicators that it’s a phishing email.
- Your Desires: Phishing emails may offer financial incentives or access to discounts or premium products.
- Your Trust: Phishing emails may appear to be from someone you know and trust. This is called “spoofing” when a cybercriminal makes the email address, signature, and content similar enough to other legitimate emails that you can’t spot the difference without looking closely.
How Can You Spot A Phishing Email?
- Check The Right Fields: If you’re unsure about an email, check the details on the email itself – specifically the “mailed-by” and “signed-by”, both of which should match the domain of the sender’s address.
- Suspicious Links: Always be sure to hover your mouse over a link in an email before clicking it. That allows you to see where it actually leads. While it may look harmless, the actual URL may show otherwise, so always look, and rarely click.
- Spelling and Grammar: Modern cybersecurity awareness comes down to paying attention to the details. When reading a suspicious email, keep an eye out for any typos or glaring errors. Whereas legitimate messages from your bank or vendors would be properly edited, phishing emails are notorious for basic spelling and grammatical mistakes.
- Specificity: Another point to consider is how vague the email is. Whereas legitimate senders will likely have your information already (such as your first name) and will use it in the salutation, scammers will often employ vaguer terminology, such as “Valued Customer” – this allows them to use the same email for multiple targets in a mass attack.
- Attachments: Phishers will often try to get you to open an attachment, so, if you see an attachment in combination with any of the above indicators, it’s only more proof that the email is likely part of a phishing attempt.
Advantage Industries Will Help You Understand Phishing
If you learn only one thing from this article, it should be that phishing doesn’t rely on digital security vulnerabilities or cutting edge hacking technology. Phishing targets the user, who, without the right training, will always be a security risk, regardless of the IT measures set in place.
Advantage Industries will assist you in training your staff to understand and spot phishing scams when they hit their inbox. Get in touch with us to start defending against phishing.
Click here to get started or call us at 866-443-8238 to schedule a consultation.


